
App Permissions & Cross-Promotion Strategies

Share to my network
In this article
Categories
Book a meeting
Connect with our team of experts to discuss your conversion and loyalty goals, and how we can help you achieve them faster.
Get a demoUsing canOpenURL and Package Manager to Identify App Presence
We recently had a customer pose a question related to cross-promoting his company’s multiple apps (vs. various, unrelated apps).
“My company offers several consumer apps. We want to drive installs by cross-promoting the apps we control to current app users. How can I use App #1 to promote the install of App #2, while excluding users of App #1 who already have App #2?
There are a number of solutions to cross-promoting apps; lookalike targeting on social media, cross-promotion networks (e.g. TapJoy, Chartboost, Flurry, etc.) and in-app cross-promotion agreements between similar apps.
A possible solution to our customer’s issue is using an app’s URL scheme or the Android PackageManager to identify if an app is installed on a device. Let’s look at how it works on iOS and Android.
iOS and canOpenURL
In iOS, the canOpenURL method included in Apple’s UIApplication class is used to determine whether an app is installed that can open a given URL resource. For instance, this can be used to present new user experiences if an app is installed.
If a URL scheme is declared in your app’s Info.plist, calling canOpenURL on it will return either:
YES if an app that supports that URL scheme is installed.
NO if no app supporting that URL is installed or if the scheme is not declared in your app’s Info.plist.
As of iOS9, you can call this method on up to 50 URLs.
Android and Package Manager
On Android, you can determine if an app is installed by attempting to get the app’s info through the PackageManager. The PackageManager is an Android class that can be used for retrieving information related to the application packages that are currently installed on the device.
To determine if an app is installed on the device, you will need to specify the app’s package name and use the getPackageInfo method. If the app is not installed, it will throw a NameNotFoundException:
static boolean isPackageAvailable(Context context, String packageName) {
try {
context.getPackageManager().getPackageInfo(packageName, 0);
return true;
} catch (NameNotFoundException e) {
return false;
}
Potential Use Cases for App IDs
The ability to identify other apps on a user’s device might be used in a number of different ways. A brand could simply collect the information that a particular app is installed, adding to a user’s profile. A media organization with both news and sports apps could use reduce double messaging by knowing that both apps were installed, sending major sporting news to fans with the sports app, and omitting those fans from the news app version of the alert.
Our Knowledge Base details how to set a tag if user has a specific app installed, which could be used in both of these examples.
Brands could also create useful, inter-app experiences. For example, apps like Yelp and Twitter have publicly documented URL schemes, allowing apps to cross-link. Apple Maps uses Yelp in this way. When you search Apple Maps for a specific restaurant, you can open up related content within the Yelp app if it is on your device.
Yelp details how to use their own URL schemes here, and also offers some best practices.
Proceed with caution, however! A whopping 60% of app users have chosen to not download an app after discovering how much personal info the app required. Make sure to consider the value you’d bring to users through the use of their personal information, as well as the privacy policies of each operating system on which you develop.
OS Differences
Apple and Google have slightly different takes on how app developers can use the ability to interact with other applications on a user’s device, as well as how permissions are accepted.
User privacy related to apps was mentioned at Apple’s WWDC 2015 – Session 703: “The apps that a user has installed are their business. If your app is installed isn’t another app’s business.” iOS explicitly asks users to opt into push notifications and locations, but use of other functions are not as clearly spelled out when a user downloads an app.
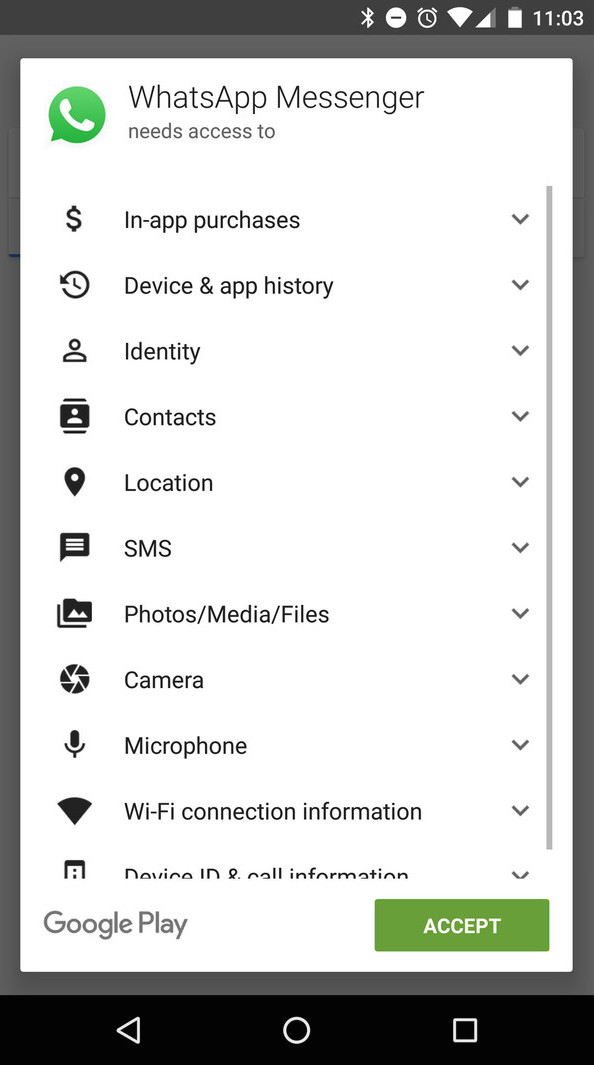
Google addresses the topic in Android Developer Resources: Interacting with Other Apps and in their Privacy Policy. “An app that collects and transmits the user’s inventory of installed apps without adequate disclosure and consent” is in violation of the Google Play Store Privacy and Security policies. Android users must accept app permissions prior to installing an app.
More About App Permissions
Check out Pew Research Center’s fascinating, interactive analysis of permissions requested by 18 popular apps on the Google Play Store.
We’re also happy to help clients, as referenced above, with strategies and questions around app cross-promotion and permissions. Contact us to learn more.
